In this article:
- Understanding the breadth and depth of cyberattack damages
- Why cybersecurity risk assessments are a great place to start when conveying the risks of cyber incidents
- How to tailor your conversation with various roles within an organization based on the specific consequences incurred by a cyberattack
- Resources for training your team once you’ve educated your team on cyber risk
In today’s fast-paced digital landscape, the risk of a cyberattack looms large, presenting a unique set of challenges for organizations across industries. However, the perception of this risk varies among employees based on their roles within the company. While the intricacies of cyber threats may not be essential for all personnel to grasp, it is crucial that every member of the team comprehends the potential dangers involved.
Unraveling the Domino Effect of Cyberattacks
The repercussions of a cyberattack reverberate throughout an organization, causing a domino effect that impacts various aspects of the business. From the scourge of ransomware to insidious phishing attempts, these malicious acts can lead to the compromise of intellectual property, trade secrets, and proprietary information, on top of financial, operational, and reputational damages.
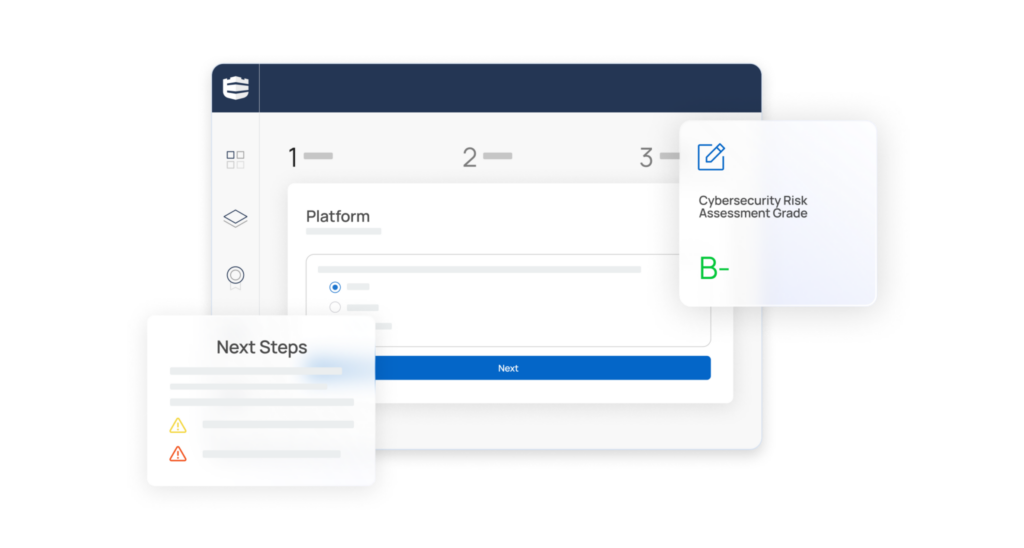
Start with a Cybersecurity Risk Assessment
Understand your cyber strengths and weaknesses by taking a cybersecurity risk assessment. This evaluation will align to established frameworks (NIST, HIPPA, and GDPR) and map your cyber health accordingly, making your conversations with other team members that much more powerful when supported by this data. The insights yielded by these assessments are invaluable, enabling you to objectively communicate the potential ramifications of an attack should the vulnerabilities identified remain unchecked.
The risk assessment also offers a baseline understanding of the organization’s current cybersecurity posture. This baseline then serves as a foundation for setting goals and plotting a trajectory toward success.
Bridging the Communication Gap
Articulating the nuances of cyberattack risks to non-IT leadership requires finesse and a strategic approach. Steer clear of technical jargon and instead, communicate in plain terms that revolve around risks, opportunities, and strategic implications. If possible, use examples specific to their role, or reference projects that might be affected in their department to make the scenario resonate that much more. By helping non-IT personnel recognize the potential consequences of a cyber-incident and how even basic preparedness can go a long way, they can more readily comprehend their role within the larger cybersecurity framework.
Crafting a Customized Narrative
Tailoring your approach to your specific audience is paramount. Below you’ll find some of the consequences specific roles might face in the event a cyberattack occurs. While it’s important to convey the gravity of the situation, we recommend avoiding fear-mongering language that might come across as threatening or unrealistic, in favor of sharing empowering suggestions of how each person can play a role in the overall defense of the organization.
Decoding Cyberattack Risks for CEOs
At the helm of any organization, the CEO shoulders the immense responsibility of leading the entire company. Cyberattacks have the potential to trigger critical disruptions to business functions, even bringing operations to a grinding halt. The repercussions cascade through the organization, eroding customer confidence and jeopardizing partnerships.
However, the implications go beyond immediate losses. The CEO becomes the face of the breach, interfacing with shareholders, customers, and board members to communicate the incident’s occurrence and share status updates. Share prices may plummet, profitability could take a hit due to remediation costs, and intellectual property theft can erode market differentiators.
Reports from Gartner point to a significant shift in responsibility when it comes to cyber-incidents. It is anticipated that by 2024, a remarkable 75% of CEOs will find themselves personally liable for such incidents, underscoring the evolving nature of cybersecurity and the need for the CEO to make it a top priority.
Navigating Cyber Risks for CFOs
The CFO’s role also comes under the shadow of cyberattack risks. Ransomware attacks, for instance, include costs beyond the ransom itself—operational downtime, investigation expenses, crisis communication, reputation-related damage, compliance fees, and lost business all add to the tally. Forensic investigations post-attack are not only expensive but also time-consuming. Recovery and remediation costs soar, likely surpassing the costs of proactive mitigation measures.
Some cyberattacks can directly hit the company’s cost centers by obstructing payment reception. Such incidents underscore the CFO’s pivotal role in cybersecurity preparedness.
Empowering Corporate Directors
Corporate directors often find themselves lacking crucial information regarding cybersecurity, making it challenging to garner the necessary buy-in. A survey conducted by the National Association of Corporate Directors (NACD) highlighted that fewer than 15% of these C-suite members expressed satisfaction with the quality of cybersecurity information provided by management. Instead of overlooking this crucial tier of leadership, remember that they often act as the liaisons between leadership and the rest of the organization and can be a major advocate for your cybersecurity initiative if they are empowered with information and resources.
Human Resources in the Line of Fire
Human resources departments function as the conduit between employees and management. HR professionals are often entrusted with enforcing cybersecurity policies and training, as well as overseeing technology and data usage. A cyberattack in this domain disrupts daily operations, necessitating crisis management. Legal obligations compel HR to notify employees of breaches and potential payroll issues.
The Legal and Compliance Balancing Act
For legal and compliance roles, the intricacies of cyberattack risks are complex. Navigating the potential legal consequences while mounting a legal defense becomes paramount. Reporting incidents to authorities and adhering to government-specific regulations like GDPR and the SEC disclosure rules within prescribed timeframes are crucial. Fines can be imposed, and breaches of contracts might occur due to presumed but unimplemented cybersecurity safeguards.
Marketing and PR: Shielding Reputation Amid Crisis
The public-facing facets of a company—marketing and public relations—are especially vulnerable in the face of a cyberattack. These departments must swiftly shift into crisis mode, dedicating resources to mitigate reputational damage. Crafting press announcements, responding to media inquiries, and tackling a barrage of calls become priorities.
The competitive landscape also shifts during a cyber crisis. Competitors might exploit the situation, claiming their services/products wouldn’t have encountered similar issues. Thus, robust cybersecurity not only safeguards the company but also bolsters its competitive advantage.
Charting the Course: From Assessment to Action
Communicating the cybersecurity risk within each role commences with a cybersecurity assessment adhering to industry frameworks. This forms the bedrock for identifying gaps in an organization’s cybersecurity posture and establishing priorities across departments.
Once it’s clear what needs to happen to bolster an organization’s cybersecurity, IT leadership needs to strategically communicate the risks of a cyberattack so that it resonates with each role. Speak in layman’s terms and share the consequences or effects unique to each role, while being careful not to overwhelm or instill fear in your audience.
Now that you’ve educated those outside the IT team on the risks of a cyber-event, it’s time to train them on how to identify malicious attacks and what to do in the case one occurs.
Here are some resources to get you started:
- 5 Tips for Implementing a Successful Social Engineering and Phishing Training Program
- How to Prevent a Security Breach in the Workplace: Building a Team of Cyber-Defenders
- Creating a Cybersecurity Culture Framework
Looking for more support with your cybersecurity program? Schedule a demo with a Defendify cybersecurity program advisor today.
Resources & insights
The 3 B's: Getting Buy-In for Data Security Policies and Procedures

A Guide to Managing the Top Cybersecurity Concerns of an IT Director

Cybersecurity Bootcamp: Get Your Security in Shape
The 3 B's: Getting Buy-In for Data Security Policies and Procedures

A Guide to Managing the Top Cybersecurity Concerns of an IT Director

Cybersecurity Bootcamp: Get Your Security in Shape
Protect and defend with multiple layers of cybersecurity
Defend your business with All-In-One Cybersecurity®.
Explore layered
security
Learn more about Defendify’s three key layers and All-In-One Cybersecurity®.
How can we help?
Schedule time to talk to a cybersecurity expert to discuss your needs.
See how it works
See how Defendify’s platform, modules, and expertise work to improve security posture.








