Though Managed Service Providers (MSPs) are trusted to build and manage IT systems and infrastructures, clients may also assume they are getting managed cybersecurity as part of the agreement. Unfortunately, not all MSPs can and do offer cybersecurity services.
While most MSPs understand the importance of having a robust and comprehensive cybersecurity program (both in-house and offered as a service), the perceived investment in time and resources needed to build such a program can be a daunting initiative.
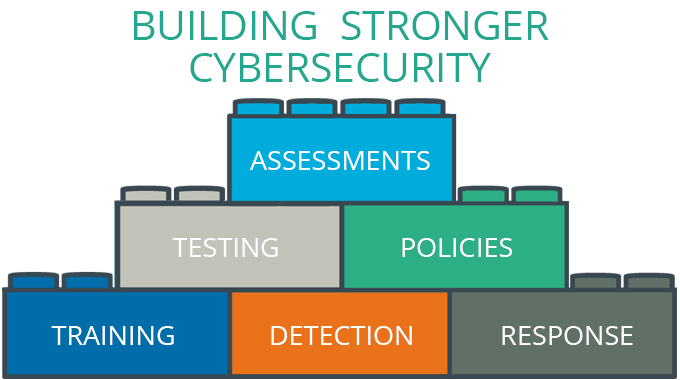
The good news is that MSPs don’t need a stack of complex technology or in-house cybersecurity experts to have a robust cybersecurity program that can extend to their clients. Here are the essential building blocks for stronger cybersecurity:
By building up a strong internal cybersecurity program, you lead by example.
Assessment and Testing
A cybersecurity assessment, with regular testing for security vulnerabilities across networks, systems and devices will provide overall visibility – and a benchmark – of current cybersecurity hygiene. This series of assessments and tests should include:
- Cybersecurity Assessment: Answer questions that map to key cybersecurity frameworks (such as NIST) to understand your risk.
- Ethical Hacking: Simulated cyberattacks (penetration test) by an ethical hacker proactively uncover network and system weaknesses.
- Network Vulnerability Scanning: Automatically searches and discovers network and device vulnerabilities, providing steps for remediation.
- Stolen Password Scanning: Identifies if employee credentials have been stolen and placed on the Dark Web.
- Website Scanning: Searches for malicious activity across your website to identify risks of hacking, blacklisting, etc.
Policies and Training
The next step to building out a robust cybersecurity program is implementing policies and training across the entire organization.
As stated in our previous blog, The Role of Human Error in Cybersecurity Breaches, employee mistakes cause approximately 88% of cyber breaches. With comprehensive policies, regular education, and awareness around cyber threats, the risk of a breach is drastically reduced. Policy and training tools should include:
- Technology & Data Use Policy: A customized policy that details employee security behavior and the use of company systems and devices.
- Phishing Simulations: Tests employee knowledge of how to spot a phishing email by mimicking real phishing attacks.
- Classroom Training: Security expert training video with quiz on key cybersecurity topics, threats, and tips to be presented in a group setting.
- Awareness Posters: Eye-catching posters that reinforce cybersecurity awareness and best practices to stay vigilant.
- Awareness Training Videos: Engaging videos sent regularly to employees show current examples of cyber threats with a learning quiz.
Detection and Response
24/7 threat detection and response is essential to keeping a strong cybersecurity posture. Detection and response capabilities require a combination of cutting-edge technology with leading cybersecurity experts who actively watch for anomalies and respond in real-time to contain attacks. This service acts as an extension of an existing in-house cybersecurity program, so MSPs don’t need to invest in one-off solutions or hire security experts. Detection and response capabilities should include:
- Breach Detection & Response: Protects devices, systems, and networks against sophisticated cyberattacks with 24/7 monitoring, containment and remediation by a team of cybersecurity experts.
- Incident Response Plan: Provides clear actions to address a cyber attack should one occur, helping to quickly minimize further damage.
- Threat Alerts: Automatic email alerts about trending cyber threats that might affect your business.
Start Building with Defendify
Defendify exists to help organizations without security teams quickly build and manage a more robust and comprehensive cybersecurity program through a single solution that delivers multiple layers of protection including assessments, testing, policies, training, and 24/7 detection and response.
MSPs can partner with Defendify to offer clients a Cybersecurity-as-a-Service option, which includes a team of Defendify security experts that help do the heavy lifting so MSPs can focus on their client’s needs.
Check out the Cybersecurity Quick Start Guide with clear steps to help organizations get started building a holistic cybersecurity program.
Resources & insights

Why You Could Be Denied Cyberattack Insurance Coverage

Cost of a Cyberattack vs. Cybersecurity Investment

Defendify Listed as a High Performer in Six G2 Grid Categories

Why You Could Be Denied Cyberattack Insurance Coverage

Cost of a Cyberattack vs. Cybersecurity Investment

Defendify Listed as a High Performer in Six G2 Grid Categories
Protect and defend with multiple layers of cybersecurity
Defend your business with All-In-One Cybersecurity®.
Explore layered
security
Learn more about Defendify’s three key layers and All-In-One Cybersecurity®.
How can we help?
Schedule time to talk to a cybersecurity expert to discuss your needs.
See how it works
See how Defendify’s platform, modules, and expertise work to improve security posture.